scdbg MemMonitorAuthor: David Zimmer Date: 02.09.11 - 7:03pm Week or two ago i added the -mm memory monitor feature to scdbg (based on libemu sctest if you havent see it) Since we are working in an emulator, we have explicit control over everything. Why not leverage that as much as we can.. So with the straight -mm mode, I made a way where by application code could have the libemu dll notify it via a call back anytime a static memory address of interest was accessed. Since all of the opcode handlers go through the main emu_memory* access functions, this was quite a clean hack. What this allowed us to do is monitor key addresses so that we can easily determine intimate details about how the shellcode was written. Such as how it goes about finding the kernel32 base address, which of the module lists it walks, and if it uses the dll base name or not. This morning I had the idea to extend this hook mechanism to also support monitoring address ranges. For each dll it supports, I added in appropirate ranges for the code portions of each library. This option is accessed through the -mdll mode. What this allows us to see, is if the shellcode is trying to patch any of the Windows API, or if it is contains hook or breakpoint detection code. Below is a screen shot showing a sample which does both. 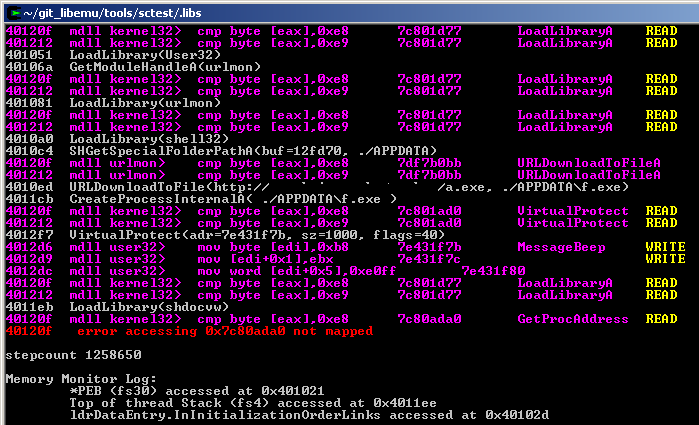
(See the main sctest mods thread for download links to source/binary) Comments: (0) |
About Me More Blogs Main Site
|
|||||||||||||||||||||||||||||||||||